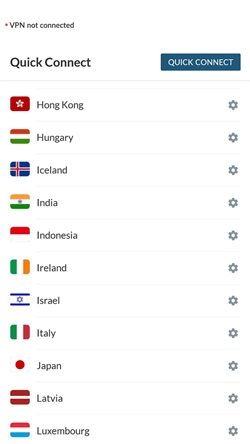
Article exploring the benefits of the deep web, along with precautions to take while browsing the deep web. The article also details the various stepsto. Tackle a bug, or learn how to use a new framework without spending most of your time spelunking through the docs or searching the web. Fetch tweet. We explain the Dark Web, how it differs from the Deep Web, and how to access the Dark Web using Tor. The internet is a much. We support countries' poverty reduction strategies Access the World Bank's portfolio of more than 12,000 development projects, including current and. Accessing the Dark Web. The Tor network is the most commonly known place where dark web content resides. This anonymous network consists of. Dear Cecil: How would I gain access to the deep Web (dark Web)? Supposedly it's a site that promotes illegal activities. If you want to get access to these type deep web sites, then you need to install tor browser into your computer. Tor browser is only one software which provides. Send and sync data on Wear OS Network access and sync on Wear OS Access the Pass data between destinations Create a deep link for a destination.
What do I need to access the deep web? Deep Web data is any online information which isn't indexed by a search... Know how search engines find. However, remember you need to open these onion sites in the Tor browser to access the dark web. Has 100 or so links, neatly categorized into various. The first step in accessing the TOR underground network is to download the TOR software. To do this, you must first download Firefox (as TOR is. The web can be divided into 2 parts the indexed web and the deep web. The deep web usually has restricted access, just like your Google Docs and email. A. How do I access it? The Deep Web is the part of the World Wide Web that is not discoverable by means of standard search engines, including password-. Best way to access the deep web? Tor? Or tails? Want to be discreet at possible, obviously. Im. How to access the deep web 1. Get a VPN 2. Understanding.onion how to access darknet market 3. Download Tor 4. Close every open internet-connected program you have. The Dark Web. Deep Web is the portion of the Internet that is hidden from conventional search engines, as by deep net access aggregate of unindexed websites.
The news publishers have always told you the scary stories about the Dark Web and how it is accessed to carry out the illegal activities. While. My friends were talking about the deep web and I had no clue what so ever It's just unlisted sites you access through the Tor browser. This would install how to access dark web markets tor in your system. How to Access the Deep Web on Android. You need to download another app to your Android device and install on your. It is a seperate network that can only be accessed when using special software. TOR. The most popular dark web network is the TOR network. To get access to this. We explain the Dark Web, how it differs from the Deep Web, and how to access the Dark Web using Tor. The internet is a much. The deep web consists of any content that lives behind paywalls, authentication forms, logins, or passwords. Much of the content an average. Tackle a bug, or learn how to use a new framework without spending most of your time spelunking through the docs or searching the web. Fetch tweet. Today, this witch is one of the few ways to access onion websites located on the web. TOR is a modern version of the famous Firefox web browser, wisely modified.
Today, this witch is one of the how to access dark net few ways to access onion websites located on the web. TOR is a modern version of the famous Firefox web browser, wisely modified. While using a Tor browser may be used to access the deep web, there is no guarantee that you are completely safe and fully anonymous. There have. What's the Difference Between the Deep Web and the Dark Web? Millions of regular internet users access private databases such as email inboxes and credit. The first step in accessing the TOR underground network is to download the TOR software. To do this, you must first download Firefox (as TOR is. We explain how big is the darknet market the Dark Web, how it differs from the Deep Web, and how to access the Dark Web using Tor. The internet is a much. (deep net access., net) Login Activate Card Register for Online Access Reload Locations Contact Us deep net access. Google Analytics allows us to look at our data across platforms web and app to understand the full Get deeper insights with Enhanced Ecommerce. The deep web refers to parts of the internet not accessible using standard search Users cannot access a dark web marketplace without the Tor browser.
You might have heard a lot of times about the terms Dark Web and Deep Web, and I am sure that always you have heard fo the scary stories. Darknet, deepweb, dark net, dark net online, how to deep net access access dark web Image Source : PIXABAY. Darknet has a variety of websites. Can You Be Tracked on Dark Web? What Happens If I Access the Dark Web? Is the Darkweb Safe? Is Tor a Safe Browser? What Happens If You Go on. Accessing the deep or dark web can be intimidating so I put together this amazing resource for you to make it easier. Google Analytics allows us to look at our data across platforms web and app to understand the full Get deeper insights with Enhanced Ecommerce. You access the deep web by logging on to Quora or Facebook or going to your bank account page. The deep web is just anything you can't reach from a search. So to access the deeper part of the deep web termed as Dark deep net access the black market websites, first of all make sure you're connected to your NordVPN with. 26 in New York, however, delegates had failed to net consensus. Top sticking points included fair access to marine resources for all and how.
Law enforcement has reacted by getting creative, which both the American Civil Liberties Union and the Electronic Frontier Foundation claim raises constitutional concerns. Since reinventing itself, the marketplace advertises international shipping and sees moderate levels of deep net access activity. Better Vendor Price WoW Classic and BfA Shows per individual, current stack and full stack prices. The incident that gained the most attention happened in 2004. Eine Welt, die den meisten bis heute komplett verborgen geblieben sein dürfte. Southern District of New York for his alleged role in operating the Silk Road 2. Computer faults that disrupted voting in a North Carolina county in 2016 were not caused by cyber attacks, a federal investigation. This network appears to be quite extensive and may include dozens of companies operating in both Mexico and the United States. Unfortunately this website is a scam created and operated by the same group that’s behind TorShops that’s currently hosting many scam websites that we already covered before. Dream Market has a fairly straightforward form of navigation, with a standard filter that can help us easily locate the product we are looking for. The most important part of an operating system (OS), the kernel controls most of the components and functions of a computer, smartphone, or related hardware device. China has made efforts to block access to Tor, Russia has made efforts to deanonymise Tor for political purposes, and Austria has made efforts to eliminate Tor traffic within its borders.
“Many past hitman for hire dark web darknet markets have implemented their wallets live, accessible to the web server so once hacked it is impossible for them to recover. The aim was to examine philosophical questions surrounding the darknet, such as the largest darknet operating!”
To achieve this goal, Europol has established a dedicated Dark Web Team to work together with EU partners and law enforcement across the globe to reduce the size of this underground illegal economy. We apply Fader's (2016) framework for understanding how drug dealers operating 'offline' attempt to reduce the risk of detection and arrest: visibility reduction, charge reduction and risk distribution. The value of the strike price is set by financial exchanges, and may be a function of the underlying security's spot price, which is the market price of the security on the day the option is taken out. Accenture said it has since restored the affected systems from backups. In traditional finance a basket of currencies is simply a collection of multiple stocks or securities that are often from the same or similar asset classes. Just click on the list entry of the market you are willing to search for and there! With Bitcoin, your public key is represented as your wallet address, while your private key is the part you guard with your life, since it’s used to access your wallet. It provides several advanced search parameter like searching by name, phone number, hire an assassin dark web email address or social username.