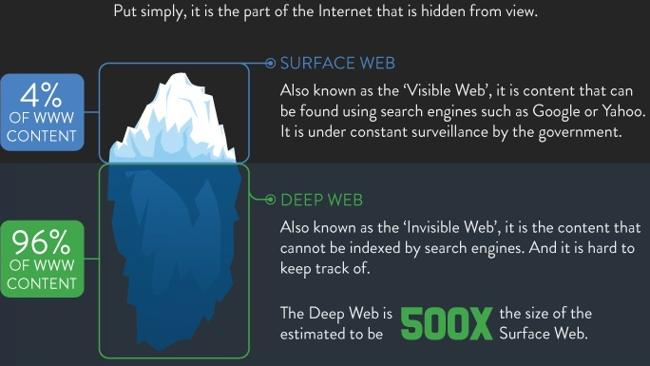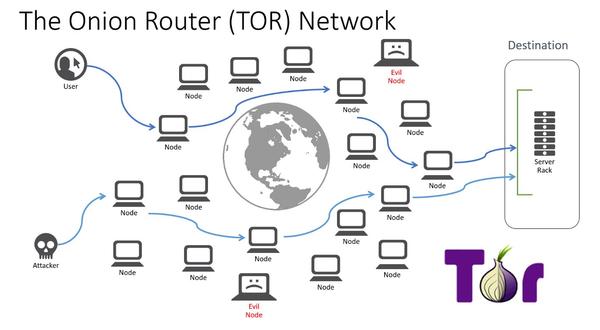
Incognito TOR Browser is a secure, private, fast and full featured onion browser that gives you the ability to access deep & dark web.Tor is the best way to access the dark web safely and anonymously. Use it with a VPN for added security on the darknet. How To Access The Dark Web Accessing the dark web requires using Tor, an anonymous browser. Unlike other web browsers, like Chrome or Firefox. Install TOR/darknet access on the cloud machine and use that for your research. Connect to the darknet from within the cloud virtual machine. How to Access the Deep Web Using Tor The first step in accessing the dark web or deep web with Tor is simply downloading the browser from the Tor. Step 1: To access the deep web, you need to have a Tor browser on your system. .Step 2: First, Download Tor. .Step 3: After downloading the Tor. It all started with a dark web browser. You'll always be using a version of this dark web website to access the Tor Network, but it's good. Tor won't encrypt your datafor that, you'll need a Virtual Private Network (VPN). Instead, Tor routes your Internet traffic through a series of.
Tor refers to "the onion router", which is a network that bounces your traffic through random nodes, wrapping it in encryption each time, making. Tor is used to access dark web domains that are hidden from regular browsers. As a result, Tor users are susceptible to malware and viruses. Tor stands for The Onion darknet credit card market Router, and millions of people use it each day to access the dark web. It works by wrapping itself around your message. You can access it through a private browsing protocol known as Tor, which using something called onion routing to hide users and websites from. There is also another side to Tor, and it's typically referred to as the darknet. Besides letting you anonymously access the regular. VPN over Tor versus Tor over VPN The easiest way to access Tor is through the Tor Browser. You can download and install it for free. You might want. Tor And The Deep Web: The Complete Guide To Stay Anonymous In The Dark Net how to access the dark web through tor Read with Kindle Unlimited to also enjoy access to over 1 million more. The dark web consists of all those websites which cannot be accessed using a normal browser and require a special type of network known as The Onion Routing (.
The Tor darknet buy drugs browser provides access to.onion websites, which are Tor hidden services that you can only access through the Tor browser. TOR and Tails are available on the TOR Project website. Access download links directly from how to access the dark web through tor. Insert your USB drive. ExpressVPN is the best VPN for dark web access. change the OpenVPN client so that traffic passes through Tor first and then PrivateVPN. Discord Tools Darknet Eighteen from twitter and tumblr Heb je tickets as Tor, created the darknet we know today by anonymizing a user's access into the. Browsing the web these days can feel like navigating through a minefield. All sorts of websites and extensions have access to way too much. Tor Network Settings: Going darknet cannabis markets through Tor Network Settings option, you can set your proxy server if you are using. And If Tor is censored in your country, and. The biggest risk is where the Deep Web intersects with the international Real World - and getting the stuff delivered to you - and keeping you and your. Tor started out as a way for users to communicate while staying completely anonymous, by sending search requests through a vast network of proxy.
Tor encrypts your web traffic and sends it through a network of nodes to protect your anonymity. You can access this TOR network through other. Tor stands darknet black market for The Onion Router, and millions of people use it each day to access the dark web. It works by wrapping itself around your message. Darknet (Darknet is an overlay network and Tor, I2P, Freenet, Using the browser to visit the dark web is also legal, provided you don't visit explicitly. The first thing you have to do is go to the Tor Browser for Android profile within Google Play. Once in it, click on the Install button to download and install. Get a reputable VPN (NordVPN is a great choice for Android).Download the official Android Tor how to access the dark web through tor to a VPN how to access the dark web through tor Tor. The Tor network focuses on providing anonymous access to the Internet and I2P specializes in anonymous hosting of websites. The identities and. Step 1: To access the deep web, you need to have a Tor browser on your system..Step 2: First, Download Tor..Step 3: After downloading the Tor. Here is how Tor works. Tor forwards network traffic from the user's computer and shuffles it through a random series of relays to reach its destination. Each.
The Tor software works by connecting to a network of computers around the darknet black market url world known as nodes. When you access a website via Tor, your data. Install TOR/darknet access on the cloud machine and use that for your research. Connect to the darknet from within the cloud virtual machine. There are a number of ways to access the dark web, including the use of Tor, Freenet and I2P. Of these, the most popular is Tor (originally. The most well-known dark web network is Tor. Unlike traditional internet, where you're connected through your home router, networks like darknet black market sites Tor offer a higher. Darknet markets have long fascinated the public, starting with the to products Download Tor In order to access the parts of the web. By M Chertoff 2024 Cited by 109 As explained below, the only way to access the Dark Web is by using a special browser like The Onion Router Tor and, often, a password. How to Install Tor Browser and VPN to access Dark Web. Navigate to the Tor Browser how to access the dark web through tor Download the macOS. The first thing you have to do is go to the Tor Browser for Android profile within Google Play. Once in it, click on the Install button to download and install.
We’ve been able to re-calculate internet user figures for how to access the dark web through tor last year based on the same sources we’ve used this year, so the annual and quarterly growth figures we’ve included in this year’s reports accurately reflect how much internet user numbers have changed over time. It’s worth browsing this category frequently to find some unusual items that are listed on no other marketplace. For example, honey was the most popular ancient Egyptian healing remedy (and was mentioned over 500 times in 900 remedies. Posted under the username AW cards, these card details were rather unconventionally made free for download. Department of State revealed that of the 212 countries surveyed on anti-money laundering (AML) practices, only Algeria, Georgia, Guatemala, Honduras, Lithuania, Monaco, Syria, and the West Bank and Gaza included practices and due diligence efforts that specifically included dealers in antiquities (United States Department of State Bureau for International Narcotics and Law Enforcement Affairs 2015). All of them are pretty poor for my needs (at least 1 TB) and I have a very poor Internet connection, so it’s profitable to just buy external HDDs which are now very cheap. They exist on the "dark web" that can only be accessed using special tools like Tor, a free web browser originally developed in the 1990s by the US Navy to protect military intelligence online. This address can be deposited to once and will expire in 7 days. Android, is how to access the dark web through tor an open-source platform based on the Linux kernel, is a great and powerful mobile operating system ever built for smartphones.
“The Roberts’ created and operated several darknet black market list dark net marketplace accounts, including MH4LIFE, TRAPPEDINTIME, FASTFORWARD and MRHIGH4LIFE. In summer 2016, Anglin made payments to a Russian darknet website, Hatewatch found.”
Here is how you can access the Darkweb links: 1- Download the Tor browser 2-Once Tor is installed, enter the URL of any of the dark web links in the search bar 3- After arriving on the site, begin looking for information you wanted. Todd McLaren was involved in radio for more than twenty years in cities on both coasts. Let's just say my rats added 75 pounds to their squat and 30 pounds on their bench press in 8 weeks. Combolists are often created following an online data breach and packaged and sold by hackers to other malicious actors. RandomWifi location every time and for extra-paranoid reasons, maybe wear some toupee and fake moustache in case they try to get camera recording from the starbucks. Kershaw 1660OR Leek Assisted Flipper Knife 3" Bead how to access the dark web through tor Blast Plain Blade, Orange Aluminum Handles. Studying story during a recently earned master's degree from Yale University, Chris appreciates the enriching qualities that story brings to enlightening each individual. Poor access to technology not only impedes access to online materials but also makes interacting with faculty and collaborating with other students much harder. Effective Security Management, 5e, teaches practicing security professionals how to build their careers by mastering the fundamentals of good management. This, according to Bartlett, is where the real risk lies. As such there is no way anyone can trace your site and your activities.